I just tried writing a exploit with ROP technique. When I searched a tool to help me finding gadgets, I found only Immunity Debugger with pvefindaddr.
But I never used it. I am lazy to learn it now (I will later). I knew msfpescan with regex option can help me but it is too difficult. Then I tried with OllyDbg. I found a nice feature to help me finding gadgets. Here what I found
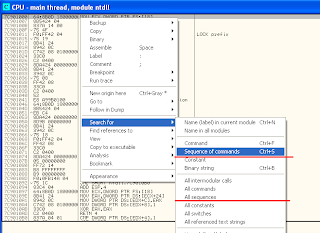
There is a search for sequence of commands when right click on CPU windows. Then it shows a dialog for typing assembly.
In this search dialog, we can use special commands and keywords. Below are what I excerpt from OllyDbg help "Search for a sequence of commands"
- R8, R16, R32 for any 8, 16, 32 bit register respectively.
- CONST for any constant
- JCC for any conditional jump
- ANY n for any 0..n commands
"Search for sequence of commands" find only one block. It is so inconvenient for us to choose a gadget. So I will show only "Search for all sequence" (the second red line of the first pic).
Let try with common gadget used for pivoting esp. I put "add esp,CONST;ANY 6;ret" to search "add esp" in ntdll.dll (on my Windows XP SP3). Here the results.
Assume We are interested "add esp, 74". Just double click it, we will see the assembly block like above pic. Then we can check if it is usable. As the above assembly code, we can use it if eax is zero.
I think this feature is nice. But I can search in only one executable module at a time :(. If someone know how to search in all modules, please tell me.;)
Tuesday, December 7, 2010
Subscribe to:
Post Comments (Atom)



you might want to use immunity for this:
ReplyDeletehttps://www.corelan.be/index.php/2011/07/14/mona-py-the-manual/
you can try :
ReplyDeletehttp://www.vnsecurity.net/2010/08/ropeme-rop-exploit-made-easy/
We have not too long ago started out any website, the knowledge an individual offer on this web site provides aided myself tremendously. Thank you regarding your entire moment & perform.
ReplyDeletebest Dns Server
This is really a nice and informative, containing all information and also has a great impact on the new technology. Thanks for sharing it
ReplyDeletegadget elettronici
Keeping in mind the end goal to get one that suits your need, you should dependably read cell phone audit before you purchase how to check airtel net balance..
ReplyDeletethis is the best
ReplyDeletekencing lancar tapi tidak tuntas dan cara mengatasinya
buang air kecil tidak lancar pada wanita dan cara mengatasinya
buang air kecil tidak tuntas pada pria dan cara mengatasinya
penyebab susah buang air kecil pada wanita dan obatnya yang alami
obat buang air kecil tidak lancar dan terasa sakit